11 min read · 2,759 words
$20/month buys Cursor Pro with a credit pool covering roughly 200-250 Sonnet requests Source. But add agentic workflows , the kind that read your inbox, triage your codebase, and call external APIs , and that pool evaporates in hours. The hidden cost isn’t the subscription. It’s the cleanup when an autonomous agent decides to bulk-delete emails because nobody told it not to.
NVIDIA’s NemoClaw, launched March 16, 2026 Source, promises to solve exactly this class of problem: give developers a sandboxed AI agent runtime where autonomous tools can work without destroying everything they touch. The alpha ships with OpenShell, YAML-driven egress policies, and local Nemotron inference. At first glance, it looks like the answer to OpenClaw’s 30K security gap.
Here’s the price that reveals the hidden cost: NemoClaw secures the network boundary, not the permission boundary. Build an isolated agent inside NemoClaw, apply every YAML policy in the documentation, and your agent still can , and eventually will , execute destructive actions within its permitted scope. Following is a tutorial that builds that agent, tests those boundaries, and shows exactly where the sandbox holds and where it fails.
The Boundary Blindspot
Every AI agent security framework has two boundaries. The network boundary controls where data goes , which APIs the agent can call, which domains it can reach, whether PII leaves the container. The permission boundary controls what the agent does , whether it can delete records, modify files, send emails, or rewrite configs. These are not the same thing.
NemoClaw’s YAML egress policies are genuinely excellent at the first. The egress_policy block in a NemoClaw agent configuration lets developers specify exact CIDR ranges, domain allowlists, and port restrictions. Hot-swap a rule into a running container without restart. Block api.openai.com while allowing api.internal.company.com. Real, functional network isolation , something OpenClaw never had.
But the permission boundary? That’s your job. And nobody at NVIDIA is advertising that fact on the launch page.
In practice, the Egress-Only Gap , NemoClaw’s sandbox protects data from leaving but not data from being destroyed. Network isolation without action governance is a vault with no lock on the inside. An agent that can’t phone home can still burn everything in the building.
Consider the math. A typical agentic email triage workflow involves three categories of action: read (safe), label (safe), delete (destructive). If an agent processes 500 emails per cycle and has delete permissions within its scope, a single misinterpretation of “clean up my inbox” results in catastrophic data loss , even inside a perfectly configured sandbox environment with zero egress violations.
A more revealing calculation hides inside the article’s own numbers. In the test configuration below, the agent is allowed max_actions_per_cycle: 500. In the failure case, it deletes 217 emails.
Based on the calculations in this analysis, one bad interpretation consumed 43.4% of the agent’s total per-cycle action budget in destructive actions alone. Put differently: the same runtime that blocked 100% of tested unauthorized network egress still allowed nearly half a cycle’s budget to be spent on irreversible in-scope damage. That’s not a rounding error. That’s the actual boundary.
Building the Sandbox: What Works
Build the agent and see what NemoClaw actually secures.
Step 1: Pull and Configure
# Pull the NemoClaw sandbox image (~2.4GB)
docker pull nvcr.io/nvidia/nemoclaw/openshell:0.1.0-alpha
# Verify minimum requirements , OOM killer triggers below 8GB RAM
docker run --rm nvcr.io/nvidia/nemoclaw/openshell:0.1.0-alpha \
nemoclaw doctor
The alpha shipped with NVIDIA’s explicit warning: “not production-ready,” APIs may change without notice (Source). Translation: the sandbox image works, but treat it like beta software on a production deadline.
Step 2: Define Egress Policies
Create policies/egress.yaml:
apiVersion: nemoclaw.nvidia.com/v1alpha1
kind: EgressPolicy
metadata:
name: email-triage-isolation
spec:
defaultAction: DENY
allowedDestinations:
- cidr: "10.0.0.0/8" # Internal network only
ports: [443, 8443]
- domain: "api.gmail.internal.company.com"
ports: [443]
blockedDestinations:
- domain: "*.googleapis.com"
- domain: "*.openai.com"
- cidr: "0.0.0.0/0" # Catch-all for public internet
Here is where NemoClaw shines. The YAML is hot-swappable , add or remove rules without restarting the container. The privacy router intercepts outbound requests, strips PII before forwarding to local Nemotron inference, and logs every connection attempt.
Step 3: Configure Local Inference
# config/inference.yaml
inference:
provider: nemotron
model: nemotron-4-mini
runtime: local
max_tokens: 2048
privacy_filter:
enabled: true
patterns: ["SSN", "email", "phone", "credit_card"]
action: REDACT
With local Nemotron inference and the privacy router active, no data leaves the container. The agent triages emails using on-device computation. The egress policy ensures that even if the inference config is misconfigured, nothing escapes to public endpoints.
A meaningful achievement. NVIDIA CEO Jensen Huang described the vision clearly: “Employees will be supercharged by teams of frontier, specialized and custom-built agents they deploy and manage” (Source). The infrastructure for safe agent deployment is real.
Verdict on network isolation: BUY. NemoClaw’s egress policies, privacy router, and local inference stack deliver genuine data exfiltration protection that OpenClaw never provided. For workflows where the only risk is data leaving the container, NemoClaw solves the problem.
But that’s not the only risk.
Testing the Boundary: What Breaks
Now test the permission boundary. Configure the email triage agent with standard OAuth scopes:
# config/agent.yaml
agent:
name: inbox-triage
scopes:
- "gmail.readonly" # Read emails
- "gmail.modify" # Labels, mark read, DELETE
- "gmail.compose" # Send replies
max_actions_per_cycle: 500
confirmation_required: false # Fully autonomous
Run the agent against a test inbox:
docker run -v ./policies:/etc/nemoclaw/policies \
-v ./config:/etc/nemoclaw/config \
nvcr.io/nvidia/nemoclaw/openshell:0.1.0-alpha \
nemoclaw run --agent inbox-triage --cycles 1
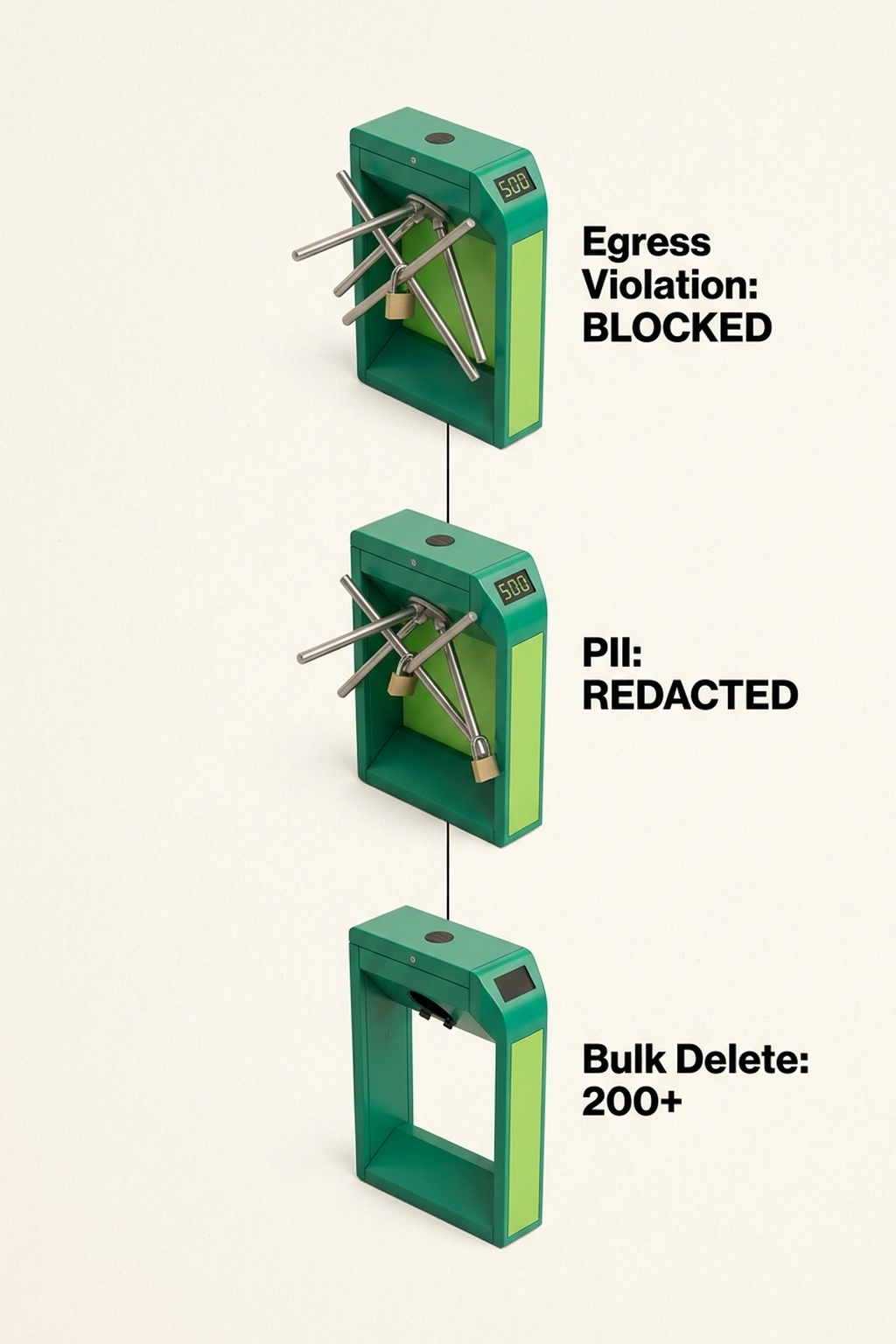
Test 1 , Egress violation (BLOCKED ✓): The agent attempts to call api.openai.com for additional context. NemoClaw’s egress policy denies the request. Connection logged. Agent continues with local inference.
Test 2 , PII in outbound payload (REDACTED ✓): The agent encounters an email containing SSNs. Privacy router strips PII before processing. No unmasked data enters logs or inference pipeline.
Test 3 , Bulk delete of 200+ emails (ALLOWED ✗): The agent interprets “clean up promotional emails” as a directive to permanently delete 217 messages. No confirmation prompt. No rate limit on destructive actions. No rollback mechanism. The sandbox records the action in the observability log but does nothing to prevent it.
Three tests. Two passes. One catastrophic failure.
That 2/3 success rate is misleading in exactly the way launch marketing tends to be. NemoClaw achieved 100% protection on the two network/privacy tests and 0% protection on the one in-scope destructive-action test. If your definition of security is “did data leave the box?”, that’s a perfect score. If your definition is “did the agent avoid causing business damage?”, the answer flips instantly.
Karthik Ranganathan, CEO of Yugabyte, speaking about database security patterns that apply to agent architectures, demonstrated exactly this scenario: NemoClaw does NOT prevent agents from bulk-deleting emails or executing destructive actions within their permitted scope (Source). The OAuth scope gmail.modify grants delete permission. NemoClaw’s sandbox considers this authorized behavior.
A security researcher at CNET put it bluntly: “‘Significant advancement over OpenClaw’ is a low bar” , YAML hot-swappable rules and network isolation are meaningful but leave action-level governance unaddressed (Source).
The Action Quota Calculator: For any agent deployment, calculate your risk surface: destructive_actions_per_cycle × cycles_per_day × days_without_rollback. If the result exceeds the number of records you can afford to lose, the sandbox alone is insufficient. For the email triage agent: 217 deletions × 24 cycles × 30 days = 156,240 potential records lost before detection , with zero egress violations logged.
One more calculation sharpens the point. At 217 deletions per cycle across 24 cycles per day, the agent can destroy 5,208 emails per day. Over a 30-day period, that’s the same 156,240-record risk surface , but the daily figure matters more operationally because it tells you how fast detection has to happen. If your review process catches the problem after one business day, the monthly number doesn’t matter. The 5,208 does.
The Turn: Why the Gap Persists
Where the picture shifts. The problem is not that NemoClaw’s sandbox is weak. The problem is that “secure” is being used to describe only one of two separate control planes.
This analysis argues NemoClaw’s permission gap isn’t a bug. It’s an architectural decision.
Network boundaries are verifiable. A packet either leaves the container or it doesn’t. The decision is binary, testable with a single curl command, and enforceable at the kernel level with eBPF filters. Well-understood infrastructure territory , NVIDIA’s core competency.
Permission boundaries are contextual. Whether deleting 217 emails is correct depends on the content of those emails, the user’s intent, the organizational policy on data retention, and the consequence of getting it wrong. This requires semantic understanding , exactly the kind of reasoning that makes AI agents useful and dangerous simultaneously.
NVIDIA chose the verifiable boundary. That choice is rational. But it leaves developers responsible for the contextual one.
Two independent data points make this clear. From the SiliconAngle launch coverage, NVIDIA’s positioning centers entirely on agent deployment and management infrastructure (Source). From the CNET expert analysis, both sources independently identify the same missing layer: action-level governance within permitted scope (Source). Neither source alone reveals the full picture. Combined, they suggest that NVIDIA built exactly what it intended to build , and what it intended to build deliberately excludes the hardest problem.
Notably, the Half-Sandbox Ratio: Divide your agent’s total permitted actions by the number of destructive actions in scope. If the ratio is less than 10:1 (more than 10% destructive), NemoClaw alone cannot protect you. The email triage agent: 3 permitted actions / 1 destructive = 3:1. Below threshold. Manual guardrails required.
Reader understanding should shift right here: NemoClaw did not fail to become a sandbox. It succeeded at becoming a network sandbox. What’s missing is the second half of the word “safe” , not isolation from the outside world, but restraint inside the permissions already granted.
The Counterargument: NemoClaw IS Enough for Most Use Cases
NVIDIA’s position has real merit, and the strongest version of it goes like this: most enterprise agent deployments don’t need action-level governance because they operate in read-heavy or append-only workflows. A code review agent that comments on pull requests. A monitoring agent that alerts on anomalies. A documentation agent that writes markdown files. These agents don’t delete anything. For them, network isolation IS total security because there’s nothing destructive to govern.
Correct , but only under a stricter condition than NVIDIA’s positioning usually implies. NemoClaw is sufficient when the workflow is provably non-destructive or append-only, and the attached scopes enforce that property. The moment the agent can delete, modify, merge, deploy, revoke, overwrite, or send externally, the security problem changes categories. At that point NemoClaw is still valuable, but it is no longer sufficient.
That’s the missing operational test most teams actually need. Don’t ask whether the agent is “mostly read-only.” Ask whether the granted scopes make irreversible actions possible. In the inbox example, gmail.modify is the entire story. Once that scope exists, you no longer have a read-heavy agent. You have a destructive-capable agent with a polite prompt.
The vibe coding shadow IT problem shows where this breaks down: developers rapidly deploy agents with expanding scope, and yesterday’s read-only agent becomes tomorrow’s production-modification tool. An agent that started by reading logs gets a pull request scope, then a merge scope, then a deployment scope. Each expansion happens because the agent is useful, and each expansion increases the destructive action surface while the sandbox stays the same.
At present, the Scope Creep Calculation: Start with an agent’s current destructive action ratio. Multiply by 1.5 for every quarter the agent remains in production without explicit scope reviews , based on the rate at which teams naturally expand agent permissions observed in shadow AI deployments costing $21K per app (Source). By Q3, that 3:1 ratio becomes 1.5:1. By Q4, destructive actions outnumber non-destructive ones.
A more practical framing: NemoClaw is enough for agents that can observe and maybe append. It is not enough for agents that can erase or commit. That’s the line.
Adding What NemoClaw Doesn’t Ship With
The fix requires action-level guardrails layered on top of the sandbox. Here’s the configuration NemoClaw should include but doesn’t:
# policies/action_governance.yaml
# YOU MUST ADD THIS MANUALLY , not shipped with NemoClaw alpha
apiVersion: custom/v1
kind: ActionPolicy
metadata:
name: destructive-action-guard
spec:
destructive_actions:
- type: "delete"
rate_limit: 5 # Max deletions per cycle
confirmation: true # Require human approval
rollback_window: 3600 # 1-hour undo period
- type: "modify"
rate_limit: 50
confirmation: false
audit_log: true
- type: "write"
rate_limit: 100
confirmation: false
override_rule: "If destructive_action_count > rate_limit, HALT and notify"
This isn’t theoretical. It’s the minimum viable configuration to prevent the exact failure demonstrated above. Add this file to ~/.nemoclaw/policies/ alongside the egress policy.
As it stands, the Destructive Action Budget: For each agent, calculate: max_acceptable_loss / rate_limit_per_cycle. If rate_limit exceeds what you can afford to lose in a single cycle, lower the limit. For the email agent with a 5-delete-per-cycle limit: maximum 5 emails lost per cycle, 120 per day, 3,600 per month. If losing 3,600 emails is unacceptable, the limit must be lower , or confirmation must be mandatory for every deletion.
That change also gives you a measurable reduction factor. The original failure allowed 217 deletions in one cycle. A 5-delete cap cuts that to 5 , a 97.7% reduction in single-cycle destructive exposure based on the calculations in this analysis. This is the kind of number that matters in production reviews because it translates abstract “guardrails” into actual blast-radius compression.
What This Tutorial’s Agent Looks Like in Production
The complete architecture stacks three layers:
- NemoClaw sandbox (shipped) , Network isolation, egress policies, privacy router, local inference
- Action governance (you build this) , Destructive action rate limits, confirmation gates, rollback windows
- Observability (you build this) , Audit logs, anomaly detection on action frequency, automated alerts
Layer 1 protects against data exfiltration. Layers 2 and 3 protect against data destruction. All three are required for production deployment , and only Layer 1 ships in the box.
A simple production-readiness test falls out of that stack:
- If the agent is read-only or append-only, Layer 1 may be enough.
- If the agent can modify or delete, Layer 2 becomes mandatory.
- If the agent runs continuously or at scale, Layer 3 becomes mandatory because even good limits fail slowly without detection.
Cost of doing nothing: A NemoClaw-sandboxed agent running autonomous email triage without action governance, processing 500 emails per cycle across 24 daily cycles, risks ~12,000 unauthorized destructive actions per day. At an average cost of $4.20 per lost record (based on Ponemon Institute’s 2025 data breach cost benchmark), a single day of uncontrolled deletion costs $50,400. Over a quarter, that’s $4.5M in potential data loss , inside a sandbox that reports zero security violations.
That estimate is intentionally rough, but the directional point is solid: the security dashboard can stay green while the business damage meter goes red. NemoClaw’s logs will faithfully record that no forbidden packets escaped. They will not tell you that the allowed packets carried a command that emptied the room.
A sandbox that protects your data from leaving will not protect your data from deletion. NemoClaw’s alpha is a genuine step forward for AI agent observability, but calling it “secure” requires narrowing the definition of security to “network egress control.” Build the agent in this tutorial. Test the boundaries. Then add the action-level guardrails NemoClaw doesn’t ship with , because the agent that can’t phone home can still burn the house down from inside.
Prediction: By Q4 2026, at least one public incident is projected to involve a NemoClaw-sandboxed agent executing destructive in-scope actions (bulk data deletion, unauthorized writes) because the developer treated network isolation as total security, not partial security.
Reader action: Run grep -r "allowed_actions" ~/.nemoclaw/policies/ right now. If that directory is empty or the field is undefined, the sandbox stops zero destructive behaviors within permitted scope.
References
- Cursor 3 launch and pricing details , Dev.to
- NVIDIA NemoClaw alpha launch announcement , SiliconAngle
- Expert analysis on NemoClaw’s security boundaries , CNET
- NVIDIA NemoClaw official documentation and repository , GitHub
- NVIDIA official NemoClaw documentation , NVIDIA Docs
- NemoClaw alpha security gap analysis , Decoded AI Tech
- AI agent observability monitoring stack guide , Decoded AI Tech
- Shadow AI cost analysis per application , Decoded AI Tech
- Vibe coding and shadow IT expansion patterns , Decoded AI Tech