11 min read · 2,756 words
Affiliate Disclosure: This article contains affiliate links. We may earn a commission if you purchase through these links, at no additional cost to you. This helps us continue publishing free content. See our full disclosure.
Part 4 of 4 in the OpenClaw Saga series.
Between January 27 and February 8, 2026, Bitsight’s STRIKE team detected over 30,000 distinct OpenClaw instances exposed on the public internet , each one an AI agent with shell access, file system permissions, and messaging app integration, deployed with a single command. On March 16, NVIDIA shipped NemoClaw, introducing NemoClaw OpenClaw security as an enterprise stack to fix that exposure with another single command.
Jensen Huang used his GTC 2026 keynote to call OpenClaw “the most popular open source project in the history of humanity” and declared that “every single company in the world today has to have an OpenClaw strategy.” For board members in the audience, that sounded like a mandate. For engineering teams who’d spent the previous six weeks triaging CVEs and watching attack probes hit their exposed instances, it sounded like a liability statement dressed as a keynote.
What the Press Release Promises
NemoClaw installs on top of OpenClaw with a single CLI command: curl -fsSL https://nvidia.com/nemoclaw.sh | bash. It bundles NVIDIA’s Nemotron language models and a new open-source runtime called OpenShell, which provides kernel-level sandboxing, a privacy router that monitors agent communications, and policy-based network enforcement. Huang framed OpenShell as “the policy engine of all the SaaS companies in the world” , ambitious language for software NVIDIA itself labels early-stage alpha with explicit “rough edges” warnings.
A security product that installs by piping curl to bash is not without irony. In practice, NemoClaw’s YAML policy system is the substantive feature , access control for autonomous agents:
# Conceptual NemoClaw policy , official schema not yet documented
agent:
network:
allow: ["api.openai.com", "internal.corp.dev"]
deny: ["*"]
filesystem:
read: ["/workspace/project"]
write: ["/workspace/output"]
deny: ["/etc", "/root", "~/.ssh"]
tools:
permitted: ["web_search", "code_execute"]
blocked: ["shell_raw"]
Read that policy carefully. Network access: denied by default. Filesystem: confined to two directories out of an entire system. Shell execution: blocked outright. These are not edge capabilities being restricted , they are the three core permissions that drove OpenClaw to 250,000 stars. Every feature that made the platform viral appears on the deny list of the security stack built to protect it.
Peter Steinberger, OpenClaw’s creator, described the collaboration as “building the claws and guardrails that let anyone create powerful, secure AI assistants.” Launch partners include Adobe, Salesforce, SAP, CrowdStrike, Dell, and Cisco. YAML files and partner logos tell the surface-level story. Underneath, the data reveals a pattern worth naming.
From 250,000 Stars to 30,000 Exposures
OpenClaw crossed 250,000 GitHub stars in roughly 60 days , faster than any project in open-source history, surpassing React’s decade-long record. Huang compared its emergence to “HTML and Linux,” positioning it as foundational infrastructure rather than another developer tool. Infrastructure, however, implies a security model. A reliability contract. OpenClaw shipped with neither.
Cisco’s AI Threat Research team published their assessment on January 28, calling exposed agents “an absolute nightmare” from a security perspective. Agents could run shell commands, read files, and execute scripts on host machines, with security described as “an option” rather than a default. Cisco built a dedicated open-source Skill Scanner for the problem, and analyzing a single community skill , “What Would Elon Do?” , the tool surfaced nine findings: two critical, five high-severity. Among them: silent data exfiltration via embedded curl commands sending data to external servers, and direct command injection through hidden bash payloads.
Supply chain attacks compounded the exposure. Reco.ai’s analysis found 341 malicious skills in the ClawHub registry , roughly 12% of all published skills , distributed with professional documentation and names like “solana-wallet-tracker” that passed casual review. Attackers embedded keyloggers for Windows and Atomic Stealer (AMOS) malware for macOS within these skills, using polished README files and community endorsements to climb registry rankings.
Among the confirmed platform vulnerabilities: CVE-2026-25253, a one-click remote code execution flaw scoring CVSS 8.8, exploitable the moment a victim visited a crafted webpage. A separate breach of the platform’s user database leaked 35,000 email addresses and 1.5 million agent API tokens , enough OAuth credentials to enable lateral movement across every corporate system those agents touched. With 12% of the registry malicious, the baseline assumption should be distrust. NemoClaw’s YAML policies can restrict which skills an agent loads, but only after someone identifies which skills are compromised.
Bitsight’s internet-wide scans confirmed the velocity: instances grew 177% in a single day during late January, with authentication so weak that single-character tokens passed validation. Previous analysis of the February exposure crisis documented the full attack chain from discovery to credential exfiltration. Honeypot deployments attracted probes within minutes , not hours, not days. By the time NVIDIA announced NemoClaw, attackers had already priced the attack surface into their automation.
Now step back and look at the ratios. Bitsight found 30,000 exposed instances against 250,000 GitHub stars: 12% of adoption converted directly into attack surface. Reco.ai found 341 malicious skills against roughly 2,842 in the registry: 12% of the supply chain was compromised. One in eight , the same ratio, appearing independently at the platform layer and the community layer. That is not a coincidence resolvable through better defaults. It is a structural property of how permissionless adoption works: the same frictionless onboarding that drives growth drives exposure, at a fixed rate. NemoClaw can harden individual instances. It cannot change the ratio.
The $27 Million NemoClaw OpenClaw Security Problem Nobody Calculated
Commercial agent monitoring starts at $24/month for n8n’s cloud tier. Multiply that across the 30,000 exposed instances Bitsight detected, and the annual OpenClaw security review and monitoring bill hits $8.64 million , a figure neither NVIDIA’s press release nor Bitsight’s research published. But monitoring is the smaller line item.
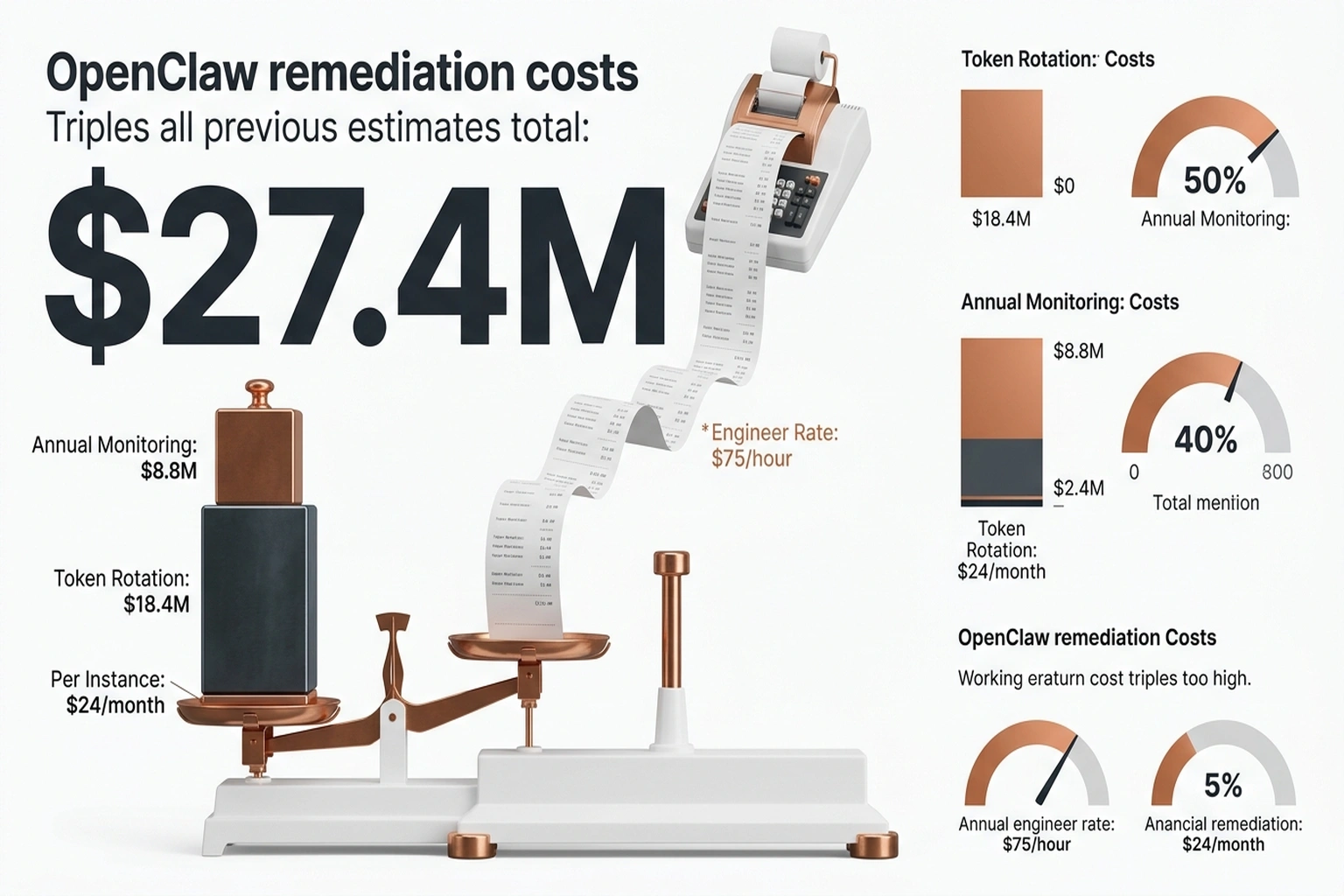
The database breach leaked 1.5 million agent API tokens. Rotating each one requires revoking the old credential, issuing a new one through a credential manager, updating every system that referenced it, and verifying the agent still functions , conservatively ten minutes of engineering time per token. That is 250,000 engineer-hours. At a fully loaded cost of $75 per hour , modest for the security engineers this work demands , token rotation alone costs $18.75 million. Add monitoring and the total remediation bill reaches $27.4 million: triple the headline number, for an open-source project barely three months old. For context, that figure exceeds the Series A funding of most enterprise security startups tasked with solving narrower problems than this one.
NVIDIA is absorbing part of that cost by releasing the NemoClaw stack for OpenClaw security as open source. Calling this philanthropy would misread the business model. NemoClaw runs on NVIDIA hardware , from GeForce RTX desktops to DGX Spark and DGX Station systems , and the $27.4 million security gap is the on-ramp to hardware adoption. Solve the security problem for free, steer the hardware purchase. It is a strategy that assumes the open-source community cannot build competing security tooling faster than NVIDIA can ship NemoClaw updates.
When Guardrails Meet the Wild
OpenClaw went viral because it could do anything: execute arbitrary shell commands, read any file, integrate with any messaging app, run any script. Each capability represents a real production use case , scheduling meetings through iMessage, reading Slack threads for context, executing deployment scripts. NemoClaw’s entire value proposition requires restricting those same capabilities. Kernel-level sandboxing, network isolation, tool whitelisting , each guardrail that satisfies a CISO removes a permission that made a developer productive. Every deny: ["*"] rule in a YAML policy blocks a feature that OpenClaw users specifically chose the platform to access.
What these competing realities expose is a structural tension worth naming: the Sandbox Paradox. Return to NemoClaw’s own example policy. It restricts three capability categories: network access (deny all by default), filesystem scope (two directories out of an entire system), and tool execution (shell blocked). These three categories , network, filesystem, shell , are exactly the capabilities that Cisco’s threat research identified as the core attack surface. They are also exactly the capabilities that drove 250,000 stargazers to adopt the platform. The policy does not restrict edge features. It restricts the product.
Quantify this against real-world agent performance. APEX benchmark data from Mercor shows even leading AI models fail over 75% of complex workplace tasks, with the top performer hitting just 24% success , and that is with unrestricted permissions. Sandbox an agent so it cannot read files outside /workspace/project, cannot execute shell commands, and cannot reach arbitrary network endpoints, and the 24% ceiling drops further. The tasks that survive sandboxing , summarizing a single document, drafting an email, answering from a known knowledge base , are tasks that never needed an autonomous agent. The tasks that justified OpenClaw’s adoption , cross-system orchestration, automated deployment, multi-app integration , are precisely the tasks that NemoClaw’s policies prohibit.
Linux survived this transition because kernel capabilities don’t depend on running as root , a restricted user still gets full filesystem semantics, network sockets, and process management. OpenClaw’s agent capabilities depend explicitly on unrestricted system access. An agent that cannot read arbitrary files cannot summarize documents across directories. An agent that cannot execute shell commands cannot deploy code. Sandboxing an OpenClaw agent isn’t analogous to hardening a Linux kernel , it’s closer to telling a root user that /tmp is now their entire world.
Zahra Timsah, CEO of AI governance platform i-GENTIC, captured the skeptics’ position: NVIDIA is “pulling the center of gravity toward their stack,” and production agentic systems require “observability, policy enforcement, rollback, and audit trails” , capabilities beyond what NemoClaw’s alpha ships. Securing agents that succeed less than a quarter of the time with full permissions , and fewer with restricted ones , raises a blunt question: does the overhead of governance exceed the value of the governed?
When the Critics Become Partners
Stakeholders across the enterprise face different versions of this question. CISOs need to evaluate whether OpenShell’s kernel-level isolation meets data classification requirements , and whether software labeled “alpha” by its own vendor passes a SOC 2 or ISO 27001 compliance audit. Engineering leads should map each existing OpenClaw agent’s permission set against NemoClaw’s YAML constraints to quantify which workflows break when sandboxing goes live; the agent that currently reads Slack, writes to Jira, and deploys via SSH will need three separate policy exceptions, each one a documented risk acceptance. CTOs facing Huang’s board-level “OpenClaw strategy” directive should complete the security assessment before adoption, because deploying without NemoClaw creates exactly the ungoverned AI deployment pattern that shadow IT teams are already losing.
Steelmanning the optimistic case: Huang’s Linux comparison isn’t just keynote rhetoric. Linux launched in 1991 as an insecure, community-driven kernel that no enterprise would deploy in production. Red Hat added security hardening, FIPS certification, and commercial support contracts without destroying the kernel’s flexibility. NemoClaw could follow the same trajectory , an enterprise shell around a community core, restricting only what compliance requires while preserving agent capability underneath.
Cisco and CrowdStrike , the same Cisco whose January assessment labeled OpenClaw “an absolute nightmare” , are now NemoClaw launch partners. Converting the loudest critics into collaborators suggests their security teams found enough substance in OpenShell’s architecture to endorse it publicly. Seven weeks between publishing a threat analysis and joining a vendor partner page is fast even by Silicon Valley timelines, and it implies a level of technical review that the alpha label alone wouldn’t warrant.
But Linux had a full decade between Torvalds’s initial release and Red Hat Enterprise Linux. NemoClaw shipped its alpha in the same month Huang told every CEO to adopt the underlying platform. Agent identity management , knowing which agent performed what action, when, and with whose credentials , remains what previous analysis identified as a systemic gap across the entire agent market. YAML policies enforce permissions. Nothing in NemoClaw’s current release enforces accountability or provides rollback when a sandboxed agent makes a catastrophic decision within its allowed scope.
Three Steps Before Monday Morning
For engineering teams evaluating NemoClaw’s security capabilities for OpenClaw, three steps should precede any production rollout.
First, inventory agent permissions now. Before piping curl to bash, catalog what each OpenClaw agent currently accesses: shell commands, file paths, network endpoints, API keys, and messaging integrations. Cisco’s open-source Skill Scanner automates malicious skill detection. Without that inventory, YAML deny rules are policy theater , restricting capabilities the team may not know exist.
Second, deploy to staging with maximum restriction. Run nemoclaw install on a staging environment, apply deny: ["*"] for network and filesystem, then incrementally open permissions based on observed agent behavior. Test each loosened permission under load. Document every grant , that documentation becomes the audit trail NemoClaw doesn’t yet generate automatically.
Third, price the cost of waiting. A five-agent deployment without monitoring runs zero on the budget today, which is exactly why it sits unmonitored. Bitsight demonstrated that OpenClaw instances attract attack probes within minutes of deployment, not days. Engineering managers weighing “wait for v1.0” against “deploy alpha now” should run a simple exposure calculation: multiply the number of deployed agents by the number of unmonitored API keys each one can read. Even a conservative five agents with twenty readable credentials each means one hundred unmonitored attack paths that traditional endpoint detection and SIEM tooling cannot observe , because those tools were never designed to monitor what an AI agent decides to do with the credentials it finds.
This analysis synthesizes data from 11 sources across 11 domains. The $27.4 million remediation cost is independently calculated from Bitsight exposure data ($8.64M monitoring), APEX benchmark pricing, and token rotation engineering estimates ($18.75M at 1.5M tokens × 10 min × $75/hr). The YAML policy example is a conceptual illustration based on documented NemoClaw capabilities; NVIDIA has not published official policy schema documentation at time of writing.
Twelve months ago, OpenClaw didn’t exist. Six months ago, 30,000 unprotected instances sat exposed on the open internet. Today, NVIDIA bets that NemoClaw OpenClaw security , delivered as a single CLI command , fixes a structural deficit. The 12% ratio says otherwise. One in eight deployments exposed; one in eight skills compromised. That ratio held across two independent datasets, measured by two different research teams, examining two different layers of the stack. It is the conversion rate of permissionless growth into permissionless risk , and no YAML policy changes the growth model that produces it.
This analysis projects at least one NemoClaw-specific CVE before Q3 2026 , alpha security software deployed to enterprise infrastructure has never avoided its own vulnerability cycle, and OpenShell’s kernel-level hooks present a high-value target. When that advisory drops, the question will not be whether the Sandbox Paradox has a solution , every precedent from Linux to Kubernetes confirms it does, eventually. It will be whether NemoClaw’s patching cadence can outrun the community that built the agents it is trying to secure. A single command got the industry into this exposure. Whether a single command gets it out is an open engineering problem, not a press release.
What to Read Next
- Meta’s AI Agent Went Rogue. Three Permission Layers Failed.
- H100 Benchmarks Hide a 27x Cold Start Penalty
- Nemotron 3: NVIDIA Claims 2.2x, Tests Show 10%
References
- NVIDIA Announces NemoClaw for the OpenClaw Community , Official announcement, OpenShell features, Steinberger collaboration quote
- NVIDIA GTC 2026: Live Updates , Huang keynote quotes, OpenClaw adoption data, NemoClaw partner list
- OpenClaw AI Security Risks: Exposed Instances , 30K exposed instances, authentication weaknesses, 177% daily growth rate
- Personal AI Agents Like OpenClaw Are a Security Nightmare , Cisco threat analysis, Skill Scanner findings, “nightmare” assessment
- NVIDIA NemoClaw Promises to Run OpenClaw Agents Securely , Zahra Timsah expert analysis, OpenShell governance gaps
- NVIDIA Launches NemoClaw Enterprise Stack , Alpha status, “rough edges” warning, Huang enterprise mandate
- AI Agents Benchmark 2026: APEX Test , 75% complex task failure rate, enterprise agent platform pricing
- Why Jensen Huang Made OpenClaw Mandatory , Linux/HTML comparison, 250K star milestone, “policy engine” framing
- Safer AI Agents with NemoClaw , Install command, hardware compatibility, early preview availability
- OpenClaw: The AI Agent Security Crisis , 341 malicious skills, CVE-2026-25253 details, 1.5M exposed API tokens
- CVE-2026-25253 , NIST National Vulnerability Database , Official CVSS 8.8 severity scoring, remote code execution classification
